Here’s a little slop-aganda poster for you to post online or (better!) print and hang all over your hometown.
Do your part to keep those data centers guzzling and Hail Columbia!
Here’s a little slop-aganda poster for you to post online or (better!) print and hang all over your hometown.
Do your part to keep those data centers guzzling and Hail Columbia!
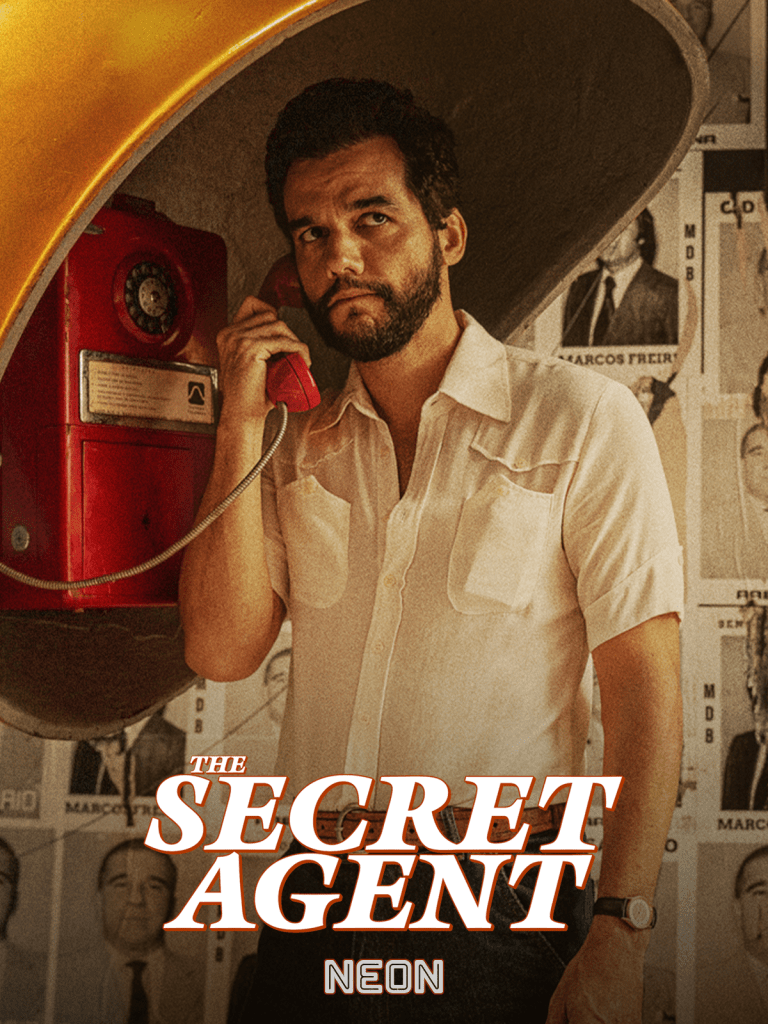
If you watch The Secret Agent at an AMC theater or similar megaplex, the odds are good that you will be forced to sit through a few commercials before the film starts. For me, before the lights went down, there was a new ad from Coca-Cola–not the ubiquitous “movie magic” couple dancing, drag-racing, and kissing through the streets, but a new one valorizing the history of bottles as though these tubes of glass have some emotional valence–and then another one, from Amazon, about a young, single Asian woman who lives alone learning how to cook ramen for herself by ordering a range of bullshit cooking accessories from Prime.
You watch these ads and they are lonely. It’s just humans, humans who are meant to live, work, and think together, standing instead alone, powerless to resist a gleaming world of products. The Products dance around our solitary heads. They assault our senses with lens flare, booming audio, bright colors, and all the other cinematic sleights of hand needed to turn a bottle of soda pop or a new slotted spoon into a life-changing, identity-affirming, spiritual revelation. We need other people to do that, and we all know it, so this–this noisy insistence that consumer products and the consumer product-driven life are beautiful and meaningful–feels bad. It feels wrong.
And then the movie starts. On the surface, it’s “about” Wagner Moura’s character fighting for his life against powerful forces that seek to silence him. Beneath that, it’s “about” the lawlessness of Brazil during the dictatorship and the vibrant resilience that percolated in the boiling kettle of that brutal state. Blah blah blah. Reflect on those Coca-Cola and Amazon ads and the film opens up a little more. This is a movie about what happens when the hand that performs the cute illusions in all of the commercials grows weary of your resistance, curls itself into a fist, and slams itself into your bleeding mouth.
Mendonça Filho wants us to think about Jaws. We come back to it again and again–in posters, drawings, a shark-tooth necklace wrapped around a villain’s throat. You may make of it what you will, but I think the shark here is the lurking danger–of death squads, brutally corrupt and murderous police, plotting executives, clutching politicians–constantly churning the water beneath our feet as we struggle to stay afloat. From the 1960s to the 1980s, the shark roared to the surface and pulled many thousands of Brazilians down into the depths, where they would never return. During that same period, the same shark terrorized the rest of Latin America, along with Southeast Asia, most of Africa, the Middle East, and other places in the world where people dared to challenge the beauty and justice of Products.
Walter Salles’ beautifully-executed I’m Still Here, from 2024,covers much of the same territory as this film, but Salles seems to think we live in a time of truth and reconciliation. Watch Bacurau, Mendonça Filho’s 2019 work (which is, I think, a better film than The Secret Agent), and you will see that the shark, the evil hunter, is still alive and well in Brazil.
It is with us, as well. That shark is the id of Coca-Cola and Amazon and all the others.

I watched this at the Capri Theater, an 85-year old movie house in Montgomery, Alabama that is positioned, for fund-raising purposes, as a sort of community arts organization. Montgomery is a town with two private Christian colleges and dozens (hundreds?) of churches the students at those colleges aspire to lead, so local arts organizations have a desperately straight line to toe. They can neither challenge the audience with dangerous art or disappoint the arts community with trash cinema. It’s no wonder, then, that they routinely program nonthreatening Masterpiece Theatre fare like this for the benefit of those who write the checks.
The Choral is a technically competent exposition of small-town English charm from the good times before the colonials turned on the metropole and everything went bad. Sure, some of the boys are off losing their arms in Flanders, but the little choral society at the heart of the film gets on with it in style and somehow ends up better than they started, transformed from a troupe of sleepy passion play performers led by a doughy middle-class pianist into an avant-garde operatic society led by a capital-A Artist named Dr. Henry Guthrie (Ralph Fiennes)* who shapes Elgar’s The Dream of Gerontius into an impassioned anti-war opera. It’s unfortunate that Hytner lavishes more attention on an awkward handjob scene between local girl Bella Holmes (Emily Fairn) and maimed veteran/tenor Clyde (Jacob Dudman) than the significant artistic process which must have unfolded to make this transition happen, but films about the artistic process rarely succeed.
Neither does this film succeed. Not anti-war, anti-class, pro-history, or pro-art, it simply moves from beat to beat, from one implied sexual tension to another, until the performance finally happens and the credits roll. I left the cinema feeling nothing about the war, about Yorkshire in the last century, Elgar, or Bach, or beautiful little British people, or the mill in their beautiful little British town, or anything at all.
Kudos to the Capri Theater for bringing more people out to see this on a Friday night than I have seen at any screening at the local AMC megaplexes in recent months. PBS knows something the art snobs don’t understand, but Capri gets it. Downton Abbey and The Choral and all the other costume pabulum that British taxpayer funds can throw at the screen have absolutely nothing to say – and that’s what people want. Cheerio.
* There is a chicken restaurant in my part of the South called Guthries, where you can get a box of chicken tenders, seasoned french fries, coleslaw, and garlic toast. Most people forego the slaw in favor of double fries, but not me. We–that is, me and at least two friends–call these things “Gut Boxes.” So, unfortunately, every time someone spoke to “Dr. Guthrie,” visions of Gut Boxes danced through my head like golden-brown sugarplums. The viewer brings to the film what they will.
Pale light falls on the
Winter jade, light the same shade
As shimmering skin
I’m posting this as a screenshot instead of embedding it because I don’t want any of their icky Meta data tracking on my website.
But look at this shit from Adam Mosseri’s Instagram.
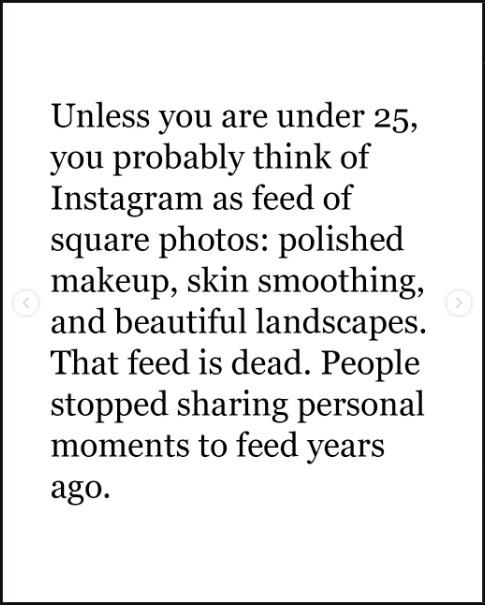
If we’re not on “social media” to see posts from friends, why are we there? Maybe the point is just to gain followers? If so, Mosseri’s got some bad news for you there, too.

They’ve got plans for you, bub. To wit: “Looking forward to 2026,” you’ll begin scrolling an endless feed of machine-generated bullshit until the dopamine drip runs dry or the Next Big Thing comes along. They believe you won’t be able to tell the difference between the machine and an actual person. And even if you can spot the difference, they believe you won’t care.
If you do care, please do this: start your own website, just like this one. Social media ate the web because it was an easy way to connect with your friends and share your ideas by building your own little website where they could find you. Now that the social media companies don’t care if you find your friends, and your ideas have to fight for space with the endless remixes generated by their machines, why hang around over there? Come build your own little website here and tell your friends to do the same thing!
Websites like this are from the past, but they are also the future. All of those “platforms” are already dying. When they are gone, this one will still be here.
Maybe the title is hyperbolic.
I love Chrome OS. I am thrilled that there is a team out there making opinionated choices about a computer user interface that isn’t just a slavish copy of Mac or Windows. I’ve been using little workhorse Chromebooks like the one I’m using to type this post for more than ten years and I will continue to use them until Google puts Chrome OS in the graveyard.
I don’t always agree with Google’s opinions about how I should use this machine, though, and I lament some of the compromises they’ve made to enforce those choices. Here are a few lamentations off the top of my head.

2. The Tote makes no sense. What is it? What goes there? Where am I toting whatever goes in there from, and where are we going? Why does it appear sometimes, but not always?
3. Some “apps” open on a new tab in the browser; others open in their own window. I’m not talking about Android apps installed from Google Play. I mean shortcuts installed as apps. Blame me. I did something wrong to make this happen; but, uh, shouldn’t it be hard to make that kind of mistake? Aren’t these things used by millions of kids for their schoolwork?
4. Google loves installing stuff on this machine without asking me. With each of the bi-weekly required and self-initiated updates, it seems, the teams at Mountain View have got some new ideas for me to try. Sometimes these ideas mean they need to install new apps, like Gemini or Google TV, and
5. Many of the useful keys people want on a computer have been replaced with useless buttons. I’ll trade the Fullscreen and Refresh buttons for the “Home” and “End” keys. Google knows this is a problem because they had to build the whole app in the screenshot down there to explain the arcane grimoire of shortcuts needed to replace the keys they decided I don’t need.
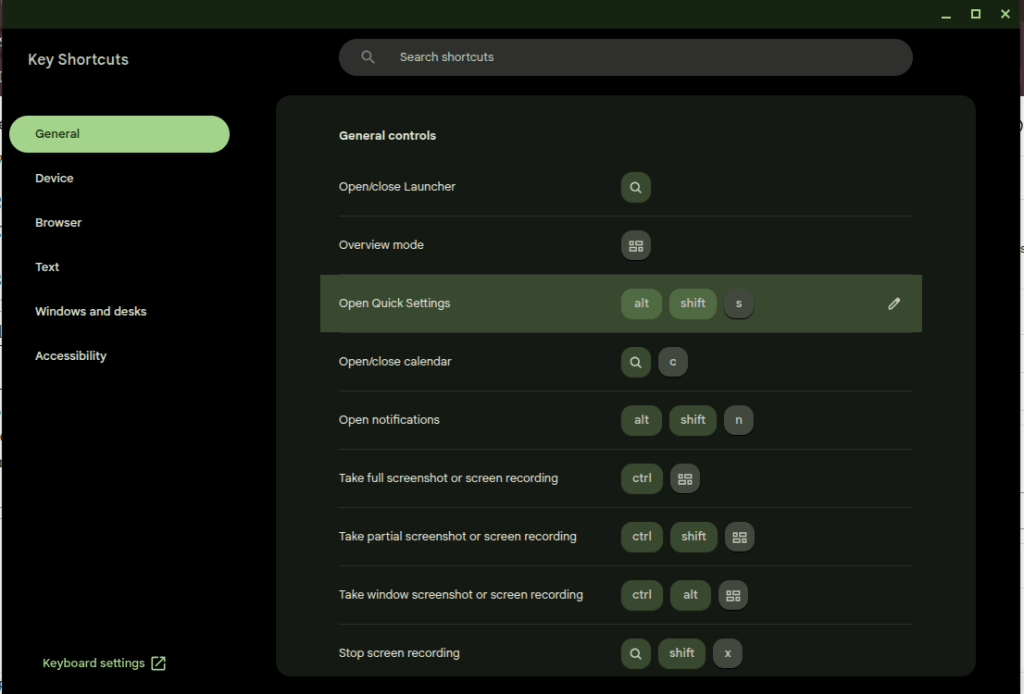
That’s enough for now. I don’t hate the player; I hate the game. I want to make my own decisions about how my computers should work, and that’s not the game for a cheap Chromebook. That’s what Linux is for, no?
Still, absolutely nothing on the desktop? Really?
I’ve been doing freelance design, taking photos, making art, building websites, and doing all kinds of stuff for more than twenty years. I’ve always thought I’d like to start a business for this stuff, but just never got up the courage to actually do it.
That changed tonight. I’m now the proud owner, er, Manager of an Alabama Limited Liability Company called Planet Glue LLC, and I have some big ideas–some old, and some new–for the company.


Right now it’s just a business card, a portfolio, a registered domain, an email address, and (most importantly?) a dream. I’ll spend the next few days building a website and some social media accounts.
When I was in grad school, I remember one day I was talking to my advisor about my plans for upcoming presentations and publications and he threw his arms in the air and shouted, “dominate!” (I love you, Dr. Frank. Never change.) That’s the energy I’m bringing to this.
I was just trying to read some “science news” (actually an article about anomalous lights appearing on a game camera in Chile), and instead I was served 6 ads at once. Glory Be.
You know? I should look on the bright side. It’s good to be informed now about Indiana University on both sides of my 32″ monitor (some good information to have here in Alabama), State Farm, AT&T, the Citi Double Cash Card, and T-Mobile. Now I can go out into the marketplace armed with all of this information and make some rational decisions.
I’m not a fan of the phrase “enshittification,” because most of this shit was just shit to begin with*, but this is a truly enormous pile of steaming dung. And it’s not as easy to fight as people would have you believe. Use an AdBlocker and they nag you. If they nag you hard enough you have to block JavaScript, and that has to be done on a site-by-site basis if you want any good JavaScript to execute.** Leave it off, and this is the reward.
What a nice world we’ve built for ourselves here.

* maybe that should be a post one of these days since I see someone pontificating about “enshittification” somewhere every day.
** is there any such thing as good JavaScript anymore? Was there ever?
I pay $20 a month for the “privilege” of editing PDFs.
I understand there are other solutions that allow me to do this for free or at a fraction of the cost. I’ve tried many of these over the years and found that Adobe’s solution works best for me as a production tool. Having reached that conclusion, I don’t mind paying for it.
Lately, however, Adobe is making it hard for me to continue paying this fee. Every time I open the app, close the app, or even just move the mouse to the wrong portion of the screen, I am bombarded with advertisements.
First there is the startup ad. The first time I open the app, every day it seems, I’m presented with a popup detailing new features I might be interested in trying. I must engage with this ad, either positively or negatively, to proceed. It’s like a little toll my brain must pay to start working with PDFs.
(Note: I had already cleared the irritating popup which prompted this post yesterday before I had a chance to grab a screenshot. I knew that if I came back today I would get a new one, and bingo! there it was.)

Thankfully I don’t need to close an ad like this every time I open the app for the rest of the day, but every time I open a document, I can be certain that another dialog recommending an AI summary will appear at the top of the screen. Let’s leave for another day the question of whether an AI summary is good for me, good for society, or whatever. Today I am irritated by the simple cognitive labor I have to do every time I open the app to work, to learn, or even just to read for fun. This dialog doesn’t obscure the document, but it consumes valuable real estate on my screen that I often can’t afford to give up. I have to think about it instead of what I’m reading.
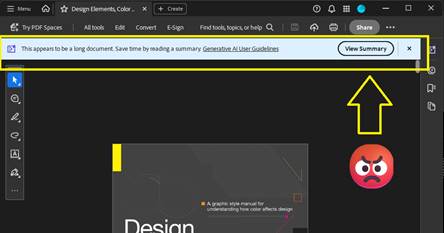
After I’ve closed this dialog, I’m still not done dealing with distractions. If I make the mistake of moving the cursor to the bottom of the screen, another dialog appears. Not only does this dialog require another little jolt of cognitive labor to acknowledge and clear the distraction, it creates a slight disincentive against moving the cursor while reading. Worse, this one obscures a portion of the document for a second or more after I move the mouse away from the Hot Zone.

There’s something else about this dialog that drives me crazy. It activates a feature that is already controlled by a button at the top of the screen.

If I wanted to use this feature, I would click the brightly-colored button at the top of the screen! This drives me crazy because the application shouldn’t just execute a command on my behalf – especially not when it has recommended the feature on startup and then reminded me of its existence again and again with popups, dialogs, and colorful buttons. Don’t treat me like a stubborn child who needs to be forced to eat his vegetables. You say you don’t like it, Adobe asks, clearly the wise adult in this exchange, but have you even tried it?
What an insult.
On this computer I pay the bills. If I want to use the damned feature I’ll damn well click the damned button.
This insult poses a philosophical challenge as well. Ask yourself: when is it OK for a machine to operate itself? The deal we’ve made with machines is simple: operators should be the ones operating them. The machine should not operate itself unless the operator has instructed it to do so, or failing to perform an operation would risk injury. When it executes a command on its own, the resulting operation should be limited in scope and duration.
Perhaps a car offers some good analogies. In my car, the headlights turn on automatically when it gets dark because I’ve turned a switch—that is, issued a command—for them to operate that way. If I don’t turn the switch, they don’t turn on. The radio doesn’t randomly change channels to introduce me to new stations (yet). It doesn’t turn on at all unless I press the button. The engine doesn’t change to Eco Mode automatically when I cross the border into a new state. The things that do operate without my explicit command, such as the automatic door locks, do so because the risks associated with error are grave. If I don’t lock the door, it may open in a crash. You can imagine the consequences. I’m willing to hand over a little piece of my autonomy to the machine here.
Does this example of remote execution, this magic AI Assistant dialog, pass that test?
In my most uncharitable moods (like the one shaping this blog post) I think about how failing to click the “Ask AI Assistant” button threatens the careers of all the managers who are responsible for driving user adoption of AI at Adobe. I suspect that Number of Impressions—that is, eyeballs on the AI Assistant feature—is a KPI they can boost by displaying this dialog at the bottom of the screen when I move the mouse down there. When I’m in these dark moods I think that’s a dirty trick to pull on me. It’s especially low down when I’ve been kind enough to allow you to reach into my bank account and automatically withdraw $19.99 every month.
Believe it or not, we’re not done with adverts yet. After capturing the screenshots for this post, I clicked the OS window control to exit the application and close the window. To my amazement, the popup below appeared because I tried to exit without saving the document. Unlike the magic AI Assistant dialog, this could have been helpful! Alas. Rather than simply prompting me to save my changes, some manager at Adobe thought this would be another fantastic opportunity to sell me on a product feature by using dark patterns to drive my behavior. “Share for review” is bright and welcoming. Simply press Enter, it suggests, and turn on the light. And that WhatsApp logo is a big green light saying Go, Go, Go. “Save without sharing,” in contrast, is dark and foreboding, like the mouth of a cave—clearly a button for dullards and dimwits to press so they can stay in the Dark Ages.

Adobe isn’t alone here. Companies are taking these liberties too often. Just today, for example, Teams informed me when I started the app that there was a brand-new Copilot feature for me to try. I have to use Teams for work, so I spend a huge portion of my life—like it or not—staring at this application. I didn’t ask for this. I didn’t opt-in, and I can’t opt-out. My employer didn’t request the feature. But, nonetheless, there it is. A group of managers and devs forced me and millions of others to just live with this thing for eight or more hours per day and hundreds or thousands of dollars per year. And if we don’t care about the feature enough to click on it, they’ll find new ways to remind us that it’s there. I expect to see more popups, more nudges, brighter colors, shimmering icons, and other ruses from the big bag of user psychology tricks reminding me to Try Copilot! until the next KPI comes along that incentivizes Microsoft to arbitrarily and unilaterally change the app again and surface new features.

I see this happening every day in web apps, mobile apps, desktop apps, even the operating system itself. And before you swing your boots up into the stirrups of your high horse, I know I can use Linux to avoid most of this. I know I can use open source tools. I’ve used Linux as a daily driver on my personal machines since 2007, and I was using open source apps before that. It doesn’t matter. If I want to put food on my table I have to use these products controlled by Microsoft, Adobe, Apple, Google, Esri, Autodesk, and all the other companies who do these short-sighted, authoritarian things to try to alter my behavior and shape my daily existence. I can’t escape it, and neither can you.
But still, if Adobe could chill with the ads in Acrobat, even just a little bit, that would be nice. Until then, I’ll be over here closing popup adverts and keeping my cursor at the top of the window.
(Edit 2/11/2026: It pleases me immeasurably that this post seems to attract bots for SEO and Sales blogs trying to build an audience. Keep those likes coming. Irony is an artifact of the past. -CBC)
TikTok is the future of web browsing. You won’t surf the web; it will be served to you “algorithmically” instead. After a while you’ll be served the content you want and it will feel like it was your idea all along.
AI is the engine to do this. The AI feed will repackage the web, all of the books, all of the recorded audio, and all of the video (which it has already consumed) and deliver it in a feed. You will open the browser and the content will appear. You will scroll and new content will appear.
This is basically the Facebook News Feed or TikTok FYP, but there is a crucial difference. Content there still leads users away from the source. People make the content (or prompt it); people (or their scripts) post the content. They need you to click on it and they want you to follow them off the feed. It’s a dialectic twisted around revenue. Facebook and TikTok want you to keep scrolling so your eyeballs roll over their ads, but Facebook and TikTok need content from users to keep you coming back. Creators who post there want you to click on their content so your eyeballs roll over their ads (or you send them money directly, but they need Facebook or TikTok to put your butt in the seat.
The AI Feed will certainly be burdened by its own internal contradictions, but it will escape this dialectic. Users will stay on the feed because it can endlessly generate content in a way that makes them feel like they’re unique, living on the cutting edge of information, and in control. Creators may post on their own sites (like this one!) but, lacking the “algorithm” and the network effects of a major platform, they will labor in obscurity. Further, the Feed will just consume their content and repackage it.
Maybe the Small Web will come back. Maybe print media will come back. I’ve explored both of those ideas in this blog at many points in the last ten years. Or maybe the AI Feed will be amazing. Who knows? The only certainty is change, change, change.